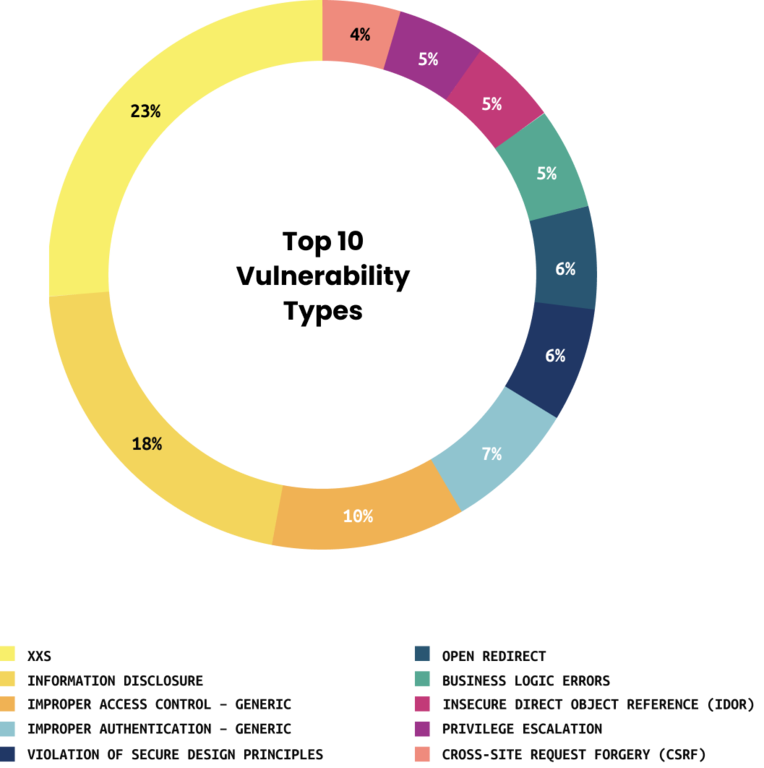
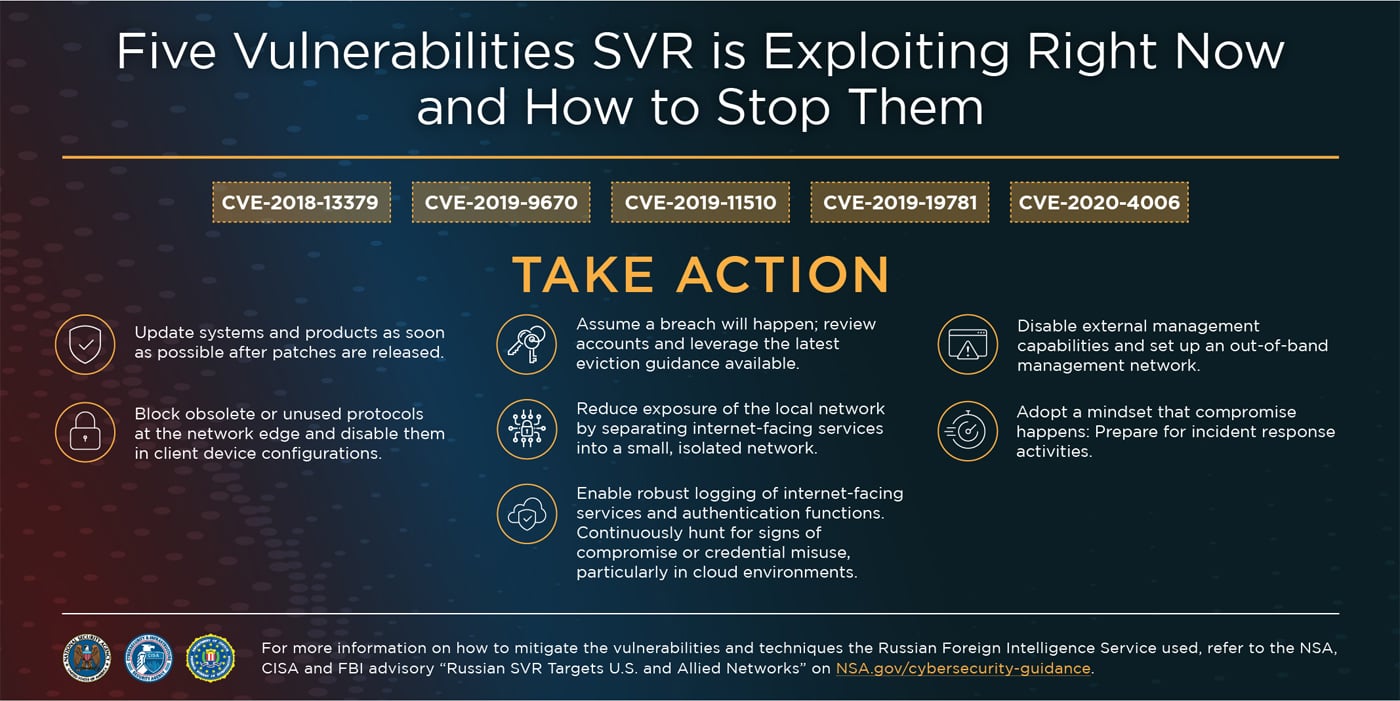
The top five vulnerabilities that could lead to a cyberattack | ITPro Today: IT News, How-Tos, Trends, Case Studies, Career Tips, More

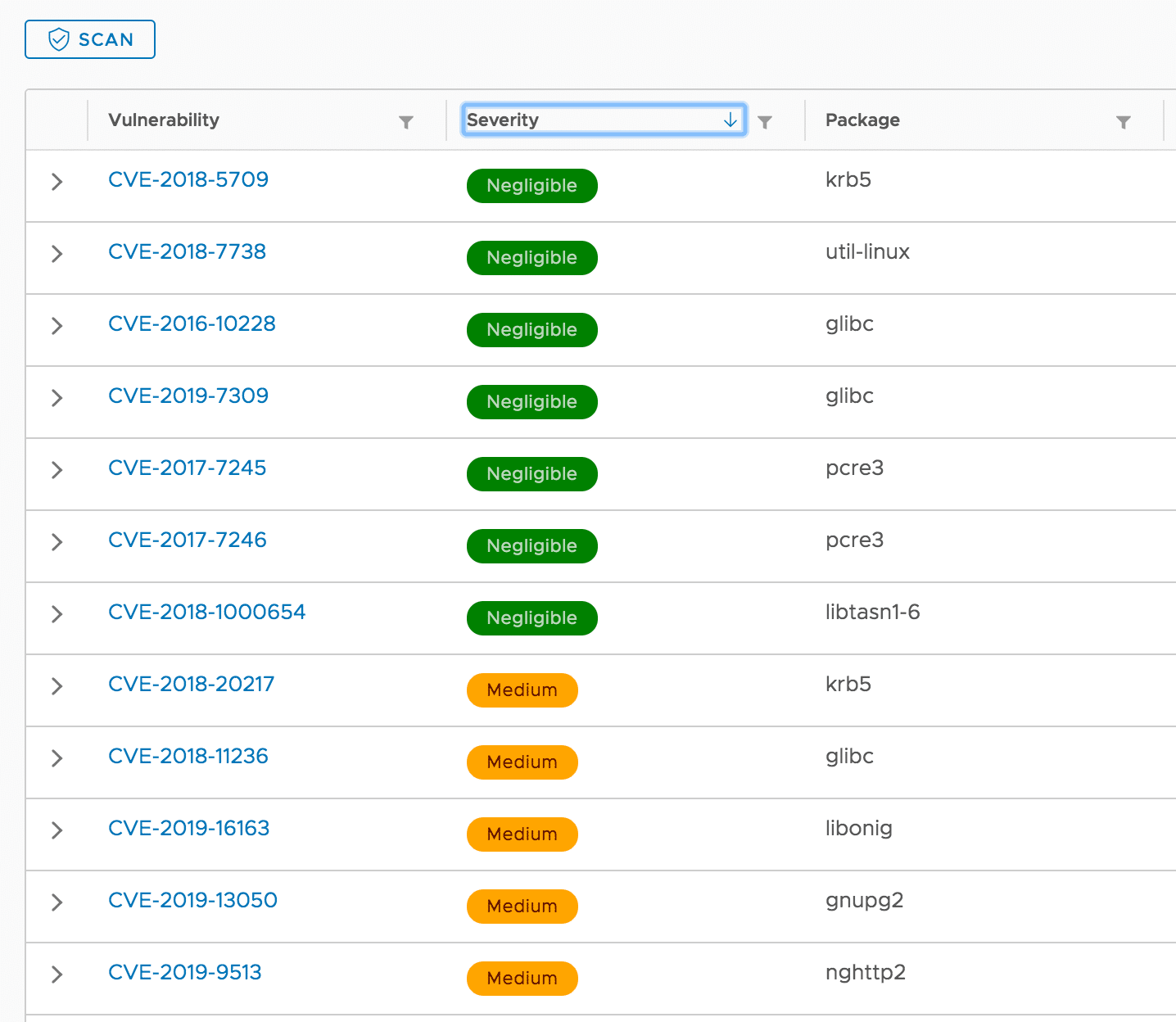
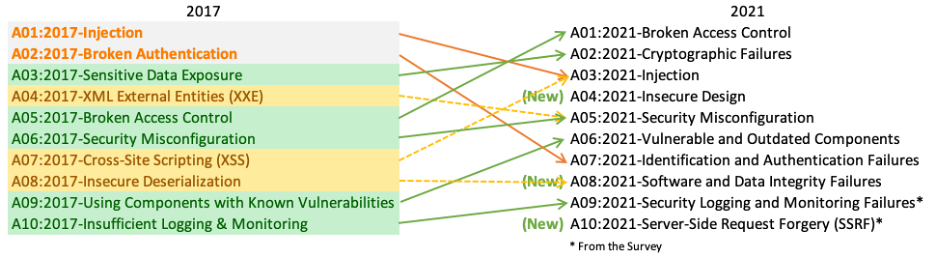
5 easy steps to improve your Spring Boot App's security | by Heinz-Werner Haas | Digital Frontiers — Das Blog | Medium